There are two types of data encryption: data at-rest and data in-transit, also known as data in motion. Data at-rest refers to inactive data not moving between devices or networks and tends to be stored in data archives. Data in-transit is data moving between devices or two network points. Data in-transit tends to be more vulnerable and requires additional security protocols to ensure data security.
Companies rely on data encryption to maintain the privacy and safety of data at-rest and data in-transit. Data encryption translates a piece of data into seemingly meaningless text that unauthorized entities cannot decipher. Each type requires specific encryption techniques for optimized protection, which we break down in detail below.
Encryption At-rest: Benefits, Drawbacks & Best Practices
At-rest data encryption protects data during storage, whether on a mobile device, computer, tablet, data warehouse, or in the cloud. This data type is a target for hackers because of its static data storage and logical structure. It typically houses valuable, private information, such as financial documents, contracts, intellectual property, and supply chain details.
Encryption for at-rest data entails encrypting stored data to prevent unauthorized access. The encryption scrambles the data into ciphertext and requires a decryption key to unscramble it into its initial state. Hackers who steal and attempt to access the encrypted data without the decryption key must override the encryption (a difficult task) to decipher the data. Without at-rest encryption, hackers load the data onto their computers and access everything.
| Benefits | Drawbacks |
|---|---|
| Provides additional security for sensitive information | Makes it difficult to recover your data |
| Maintains data integrity during hardware replacement, repair, and upgrade | Hackers sometimes discover decryption keys |
| Stretches across multiple devices and secures from in-person data theft attempts | May turn out to be costly, requiring upgrades and maintenance for optimal performance |
It’s important to know how to protect and secure data at-rest, typically stored in one location, such as hard drives, flash drives, or cloud storage. When data at-rest is encrypted through hardware-based software and devices, personally identifiable information and sensitive content are protected from unauthorized people trying to access or steal the data.
Some best practices when using at-rest encryption include the following:
File-level encryption only protects individual files, whereas full disk encryption (FDE) secures everything on a hard drive. If a hard disk is lost or stolen, all the data is secure and accessible only through the encryption key. It’s also important to note that the impact on performance is minimal. Modern FDE technology does not bog down system performance—thus, adding this technology will not significantly slow operations.
Separating the keys from the data and storing them offline, specifically in a physical location like a USB drive or hard drive, makes them less vulnerable to hackers. You can limit users’ access to the keys or rotate your keys on a schedule. In addition to safe storage, consider logging and monitoring key usage to detect unauthorized access or suspicious activity.
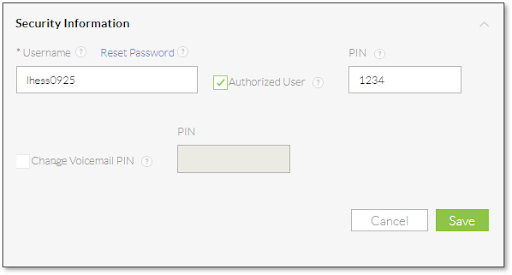
Enforce robust access protocols by adhering to best practices for username and password security. Secure login pages’ privacy by requiring strong passwords combining letters, numbers, and special characters. These practices make it more challenging for hackers to access cloud-stored data. Additionally, restricting access to specific times or days should be considered to reduce the risk of unauthorized access.
Data encryption isn’t your first or only defense. Safekeep your data properly by storing sensitive hardware in temperature-controlled rooms to prevent overheating or moisture damage and implementing access controls.
When it comes to disposal, data-wiping software must be used, and environmental regulations must be followed for disposing of electronic waste (e-waste). Also, keep hardware inventory records, including serial numbers, for auditing and compliance purposes.
Utilize mechanisms that prevent users from directly accessing sensitive data and systems during normal operations. For example, select who can directly access databases and run queries. For users who only need information without requiring direct data access, create dashboards containing relevant information and limit direct data access to a select group.
In-transit: Benefits, Drawbacks & Best Practices
Encryption in-transit protects data in motion or while it’s being transferred. Data is more vulnerable during this time and needs additional security protocols to protect it. For instance, many in-transit encryption services also include steps to authenticate the sender and receiver before decrypting the information upon arrival using Transport Layer Security (TLS), which secures the data between two apps, preventing interception or tampering.
TLS is a security layer that helps to protect data when uploading or downloading a document or media file. It also protects your business when you send an email or data packets using voice-over-internet-protocol (VoIP) business calling solutions.
Encryption doesn’t necessarily make data theft impossible—it makes it more complex and resource-consuming. That’s why data encryption in-transit and at-rest is just one of many security layers, such as access control and authentication, that businesses can use to protect valuable information. However, if best practices aren’t observed, both types of encryption have drawbacks and risks.
| Benefits | Drawbacks |
|---|---|
| Prevents data access from common hacking strategies like eavesdropping and data breach | It’s not always possible to hide metadata (sender, recipient, and date) |
| Reduces the potential attack surface for hackers | Encryption gives third parties too much security, protecting them from law enforcement and investigations |
| Prevents hackers from using data if they intercept communications | Requires cooperation to follow protocols by all parties involved |
To give a clearer picture of what data in-transit is, some examples of a file in-transit include sending an email over the internet, colleagues exchanging files over a corporate network, and transferring data from a USB to a co-worker’s laptop.
The best practices when using an in-transit encryption service include the following:
Anticipate breaches and develop data protection policies for your business, hire a data network security consultant to provide recommendations, and invest in cybersecurity insurance to protect your company from liability. Ensure you regularly monitor your systems for suspicious activity and train employees on data protection best practices, including spotting and recognizing potential security threats.
Ensure your team has implemented firewalls and network access control features to secure data transmission to and from your network. Secure your Wi-Fi network with strong passwords, and consider setting up a separate guest network for visitors and external users. Regularly monitor network traffic, particularly for suspicious activity, such as multiple failed login attempts, which may indicate unauthorized access attempts.
To protect your data further, set up spam filters, phishing blocks, and malicious file-sharing detection. Use tools like GuardDuty to automatically detect unauthorized attempts to move or access data, such as trojans trying to copy data to unknown or untrusted networks.
In addition to encryption, require strong passwords with a minimum of eight characters containing a combination of letters, numbers, and special symbols. Remind your team to avoid using personal information like their address and birthday. Passwords for high-risk accounts should be changed every 60 to 90 days. For more information, check out these three strong password tips by the U.S. Cybersecurity and Infrastructure Security Agency (CISA).
How VoIP Encryption Works
The availability and functionality of VoIP business phones have streamlined how businesses of all sizes communicate. Teams coordinate and share personal or privileged information with clients and colleagues through internet-based solutions. Therefore, all conversations over VoIP channels must be encrypted and modified into cluttered voice data packets to prevent them from being intercepted while in-transit.
Call and phone system encryption prevents terrible actors from maliciously intercepting messages and using the information. Our VoIP statistics article details that more companies are switching from traditional phone systems to VoIP because VoIP solutions increase productivity and provide cost-effective benefits.
There are three basic steps to VoIP encryption: first, it creates a secure connection during a call. Second, your audio is broken down into data packets sent through a Secure Real-time Transport Protocol (SRTP). The third step entails unpacking the packets once your message arrives at the destination. This entire process happens milliseconds between when you speak and when the caller hears you.
Here’s the summary of what happens during each step:
- Step 1—Secure Connection: First, a phone call is initiated. A secure connection is made between the two parties to begin transferring information.
- Step 2—Encryption: When you speak, VoIP breaks your voice call into data packets and sends them to the other caller using a transport protocol called Secure Real-time Transport Protocol or SRTP. This protocol encrypts the messages with AES to prevent interception and theft.
- Step 3—Decryption: Once your message arrives safely at the end destination, it’s reassembled using the decryption key. Your data packets are unpacked, and the receiver hears your voice played as audio. All this happens during the milliseconds between when you speak and your caller hears you.
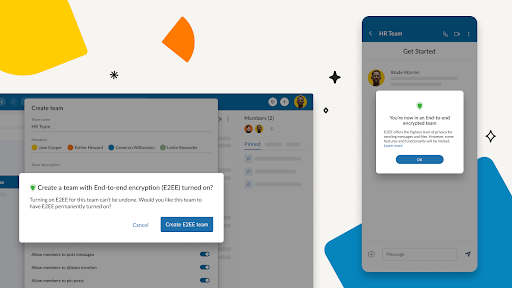
Unified communications as a service (UCaaS) uses a similar process to encrypt text messages, chat, and video conferencing calls. Encryption protocols scramble messages and make them unreadable during transit. The end-user receives and decrypts the data to use the information inside the message. When this data is warehoused, at-rest encryption comes into play to ensure it remains safe.
VoIP security is necessary because of the rise in cybercrimes. According to the 2023 Verizon Data Breach Investigations Report, 83% of breaches involved external actors, primarily from organized crime groups with financial motives. Even if your data is backed up and restored, there may be damage to your reputation and credibility that may affect your business operations.
Remember that any unencrypted or unprotected data is at risk. Instead of playing catch-up, businesses must prioritize their data and associated risks, and then build defense mechanisms before attacks materialize. Business data is stored, used, and transmitted daily. The company website, video conferencing, and email communications must be secured, but data encryption needs to be applied to all channels, including voicemails and data storage.
Examples of Encryption At-rest & In-transit
Encryption is used to secure devices such as smartphones and personal computers, protect financial transactions such as making a bank deposit and buying an item from an online retailer, and ensure the privacy of messages such as emails and texts. Below is a quick look at examples of these two encryption data states:
Encryption In-transit
Encrypting data in transit is crucial for securing data as it travels between various systems, devices, or networks. For instance, it includes data that is moving between:
- Applications
- Networks
- Computers
- Devices
- Services
Concrete examples of data in-transit include emails, messages, and files being sent or shared. Using secure socket layer (SSL)/TLS is crucial to prevent attackers or cyberhackers from accessing the data in motion. Encryption, while in-transit, protects data from eavesdropping attacks initiated by malicious entities looking to analyze traffic, specifically unencrypted data sent over the internet.
Encryption At-rest
At-rest data refers to data that is currently not being used or has arrived at their destination. Some examples of at-rest data include:
- Cloud storage assets
- USB drives and other external storage devices
- Databases
- File archives
Examples of encryption schemes that can be used to protect data at-rest include full disk encryption, cloud asset encryption, and file system encryption. These solutions typically involve key generation and industry-standard algorithms such as the Advanced Encryption Standard (AES). Using at-rest encryption helps protect businesses from attackers attempting to steal protected files, read confidential databases, and launch hardware attacks.
VoIP Providers With Both Types of Encryption
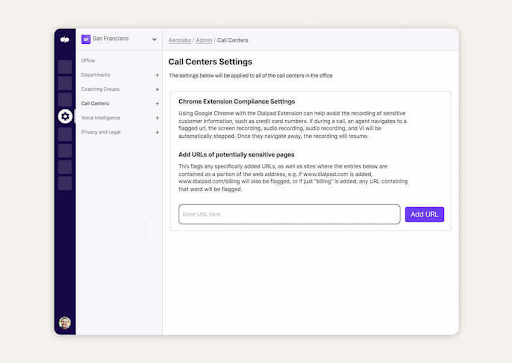
VoIP services, like other business phone systems, have certain security threats and risks. However, companies mitigate risks by choosing a provider offering secure, encrypted services. When choosing a provider, select one that provides VoIP and UCaaS security features and encryption. Additionally, there are government regulations for handling personal information, like the Health Insurance Portability and Accountability Act of 1996 (HIPAA).
The three providers listed offer data at-rest and data in-transit encryption, are HIPAA-compliant, and have protocols like physical data protection, secure communications, and breach notifications in place. This is particularly important for businesses in the healthcare industry as they need a HIPAA-compliant VoIP business phone system.
Frequently Asked Questions (FAQs)
Develop a cybersecurity plan and work with phone system providers that offer quality encryption services. Measures that must be included in your data privacy protocols include using strong passwords, enabling two-factor authentication, security protocol training, and banning the use of public connections to access sensitive information.
The General Data Protection Regulation (GDPR) is a European Union law that protects an internet user’s privacy and security while browsing websites online. However, it doesn’t necessarily require at-rest data encryption. Encryption is more than a regulatory compliance issue. It reduces the probability of a successful breach—protecting your business, employees, and clients. Protecting your data also helps you avoid costly fines and damaged trust.
Choose a VoIP provider with extensive security protocols and encryption in-transit and at-rest in addition to other essential VoIP business phone features. Furthermore, your organization is responsible for safeguarding passwords, monitoring access, reviewing call logs, deactivating inactive accounts, and using a VPN for remote staff.
If you’re looking for a VoIP provider with a 99.999% uptime guarantee and a secure calling environment, consider Nextiva. Its security features include 24/7 monitoring, biometric checkpoints, and an audited data center based on ISO certification. Read our comprehensive Nextiva Contact Center review for pricing plans and features.
Data at-rest and data in-transit encryption, AES, and Rivest-Shamir-Adleman (RSA) are the most common and trusted encryption techniques. AES is used to encrypt in-transit and at-rest data, while RSA is typically used for transmitting data between two endpoints.
Bottom Line
Understanding the importance of data encryption at-rest and in-transit drives businesses to protect sensitive information from unauthorized access and ensure confidentiality and privacy. Data is a great asset, and once you are entrusted with private information, you are responsible for protecting clients’ and employees’ data.
Data encryption at-rest and in-transit is a must-have security protocol for all online business communications, including VoIP services. Any disruption to your business phone system, such as system misuse, breaching, or theft, could be catastrophic, which is why data protection and privacy are non-negotiable. Before choosing a provider, ensure it has the encryption standards your business demands, including specific industry regulations, such as HIPAA compliance.